BeyondTrust Roundtable: Tackling Critical Microsoft Vulnerabilities
Sponsored content: Shifting from reactive to proactive security.
With the disruptions in operations caused by the COVID-19 global pandemic, most organisations in the APAC region have been prioritising keeping the lights on. “They’ve been focused on keeping operational resilience and access to resources for employees who are obviously working from home”, noted Andrew Milroy principal adviser at Ecosystem Research during a recent virtual roundtable hosted by Focus Network and Beyond Trust.
Milroy pointed out that every day, the AV-TEST Institute registers over 350,000 new malware and potentially unwanted applications (PUA) and fighting against this giant enemy with traditional, reactive cybersecurity measures is challenging.
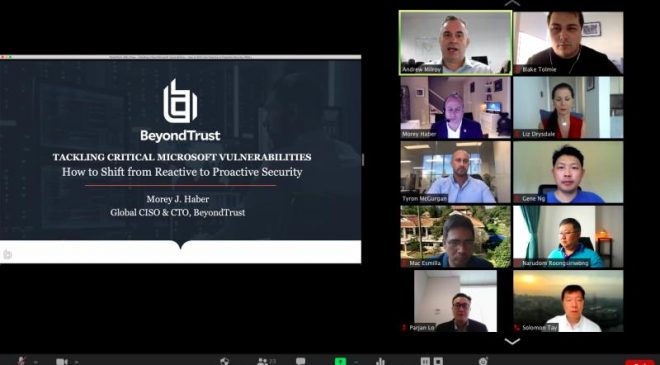
Early this month, Morey Haber CISO and CTO at BeyondTrust, and author of three books on the matter, offered his “unique perspective” at the virtual roundtable to about 20 leading CISOs and heads of IT security from Singapore, Thailand, and Indonesia. According to Haber, CIOs and CISOs are faced with their weakest links being their “users”. About 99 per cent of compromises are due to end users interacting with systems, primarily phishing attacks — they’re clicking on unknown links.
In 2020, more than 850 vulnerabilities were found in Microsoft products. The OS is full of vulnerabilities, that includes the latest Windows 10, which is used on 70.98 per cent of Windows computers as of March 2020.
The end-user is running programs they shouldn’t; and they’re basically being socially engineered to give up information or do something that could be detrimental to the environment.
Haber gave an interesting example of where an employee might get an email from human resources, requesting an update to their information — just in case there’s a COVID crisis. The employee clicks on the link thinking they are entering a standard response to update their HR information; however, they’ve clicked on a website that’s stealing their credentials.
That’s why users are a common challenge for the cybersecurity community today and considered even by Verizon’s data breach report – to be the number one attack vector.
Removing admin rights from endpoints with optimum application control
During the virtual roundtable, the discussion centred around changes to the work environment and how a CISO must tackle cyber security beyond the office building and the desktop. Which brings a whole set of challenges for privileged access security, application control, and the threats that have evolved.
According to Haber, COVID-19 and other environmental factors have people working from home posing a potentially greater risk for unsecure networks and unsecure wireless networks.
Haber noted these workers might have to be given admin rights while working from home so they can add their home printer or conduct other business-related tasks with their own machines. However, CISOs and CIOs won’t necessarily have visibility into the hardware. Other users might also be operating on a BYOD device or other types of problems that might have verifying compliance.
Kok Fong Lee SVP risk and control from Singapore DBS, noted the organisation didn’t have an issue with BYOD because it doesn’t allow outside hardware. “Remote workers anywhere or contractors use our company laptops,” he said. “We’ve been mobilising staff for many years as part of our transformation journey.”
For those who haven’t mobilised staff like Singapore DBS, many of the employees working from home and uses privileges with admin rights to do administration in the cloud, or on-premise, said Haber.
“Privileged users are at home, but they still need to log in as an administrator, or even as a database owner to perform their tasks,” he said. “Those are all attack vectors that are ripe for threat actors and represent new and evolving challenges to cyber security that we have to consider.”
BeyondTrust’s Microsoft Vulnerability Report 2020 brings key findings that shed some light in this matter.
“Microsoft announced 192 critical vulnerabilities in 2019 across every major Microsoft product, from Internet Explorer, Edge, Office, Server to workstation,” Haber stated. “[These] could have been prevented just by removing admin rights. Think about it for a minute — if I remove admin rights from end users — whether on the server, or on desktop/laptop, that I’ve issued while they’re working remotely, I can mitigate the vulnerability exploit combination for 77 per cent of these vulnerabilities.”
Haber recommends that least privilege tactics of removing admin rights from endpoints is an effective mitigation strategy, but people aren’t doing it more often because of the mistaken perception that doing so is complex and troublesome. This is also why users get secondary local admin accounts or put into admin group. “By deploying least privilege techniques people can get things done and it doesn’t become a burden on the help desk,” he said. “If I can reduce all users them to standard users, I can buy myself some time for patching and potentially mitigate those risks; especially for attacks using phishing that are using a vulnerability exploit combination.”
According to Haber the IT team are dealing with admin rights everywhere. Everything from the workstations; to automation; Cloud to remote workers; to mobile devices; and next gen technology, the placement of Microsoft technology is almost everywhere.
“When we remove admin rights as part of a mitigation strategy, we break it down by product realised that for Internet Explorer — 33 critical vulnerabilities were present; for Microsoft Edge 86; for Windows itself – 170,” he said. “There’s about 177 critical ones in Microsoft Office; and 171 across the server product line.”
Let’s talk about Windows
Mohamed Zubair, VP cyber security intelligence from GIC Pro Limited, told the virtual roundtable the organisation typically runs applications admin, and users will need admin credentials to log in and do the installation.
Organisations need to consider any Windows Seven or 2008 servers, or older systems, within the environment. The placement of the technology and the mitigation that can be gained by removing it from servers; by removing it from remote workers; by pulling it out from critical infrastructure; by not including admin rights in automation, he said.
“When you do that you find that 100 per cent of Internet Explorer vulnerabilities could be mitigated just by removing admin rights,” said Haber.
He believes there’s three main reasons why everyone isn’t doing it. The first is the perceived negative impact on end user productivity.
“People actually feel punished if you take away their admin rights, when in fact you’re trying to improve end user security,” he said. “There are tools and techniques of privileged access management that actually increase productivity.”
For example, if the end user is given two accounts; their standard login account as a standard user; and their secondary account as an ex-admin. According to Haber, they get multiple UAC pop ups during the day that requests admin credential to do their job, they spend five to 10 seconds every single time that comes up.
“The perception of negative impact on end user productivity is false. You can increase productivity by not having them type in their secondary credential and improve security by not even giving it to them in the first place,” he said.
The second reason is it’s quicker and easier to give everyone admin rights. If you throw everyone in the admin group, everybody works, everything is happy. “But you also have incredible amounts of risk, and your risk surface is massive”, said Haber.
“When you consider on-premise/off-premise Cloud, next gen technology, IoT and everything, giving everyone admin rights completely unacceptable,” Haber said. “We must find a model that works for the business where we’re only giving the administrative rights that are necessary when they need it, for only as long as they need it”.
“They continue to be productive and we don’t have this problem of making it quick and easy,” Haber said. “Just giving everyone admin rights as part of their identity governance – don’t do that. Let’s find a better way to truly manage them.”
Going from reactive to proactive
Common problems that people think about when they remove admin rights, is the potential for endless calls to the helpdesk.
Haber noted that shifting from a reactive to a proactive approach to mitigating critical Microsoft vulnerabilities means adopting least privilege and just-in-time privileged access management models that help you remove admin rights, while making it easier for people to do their job.
“I’m going to mitigate the risks from those critical Microsoft vulnerabilities to buy myself time for patching, to make sure I’m not a part of the next zero-day exploit and actually be safe from all the different types of malware threats that are out there,” he said.
The virtual roundtable took an interesting turn when Haber pointed out how adopting a proactive approach to cyber security allowed employees to be more functional and productive, but also reduced their rights at the same time. He noted that there was no downside to removing admin rights.
Explosion of privileged accounts
The adoption of new technologies has resulted in an explosion of privileged accounts. According to Haber, 20 years ago organisations only had privileged accounts in the data centre, and no-one cared if they had the password because they had to be within the building and within that network to use those credentials.
“Today we have cloud, we have hypervisors and we have IoT and we’re also embarking on DevOps processes,” he said. “We have privileged accounts everywhere and it’s an explosion that is affecting our entire universe.
From cameras to alarm systems and anything that’s network device connected – everything has a privileged account that can be leveraged for a botnet surveillance or compromise the organisation.”
According to Haber those privileged accounts need to be removed when possible. When dealing with them on endpoints — the critical vulnerabilities on Microsoft operating systems — many of them can be mitigated just by removing the end user’s interaction.
“We do this with BeyondTrust Endpoint Privilege Management solution,” he said. “It is the removal of admin rights on Windows, Mac OS, Unix, Linux, and even network devices, as side solutions. We also do password management to check-in, check-out passwords; automatic rotation; and remote access technology..”
According to Haber this is great for people that are working remotely – for contractors; employees; vendors; and those operating remotely who need to get into the organisation to interoperate with internal resources without the need for VPN.
Tags: admin rights, Application Security, BeyondTrust, Cloud Computing, Cyber Security, data breach, Data Protection, digital transformation, Governance Risk and Compliance, Identity Access Management, Microsoft



