Cofense Roundtable: How to Save Time and Resources with Advanced Phishing Automation
Sponsored content: Thursday, 11th February 2021 – ANZ
Save Time and Resources while Reducing Risk with Advanced Phishing Automation
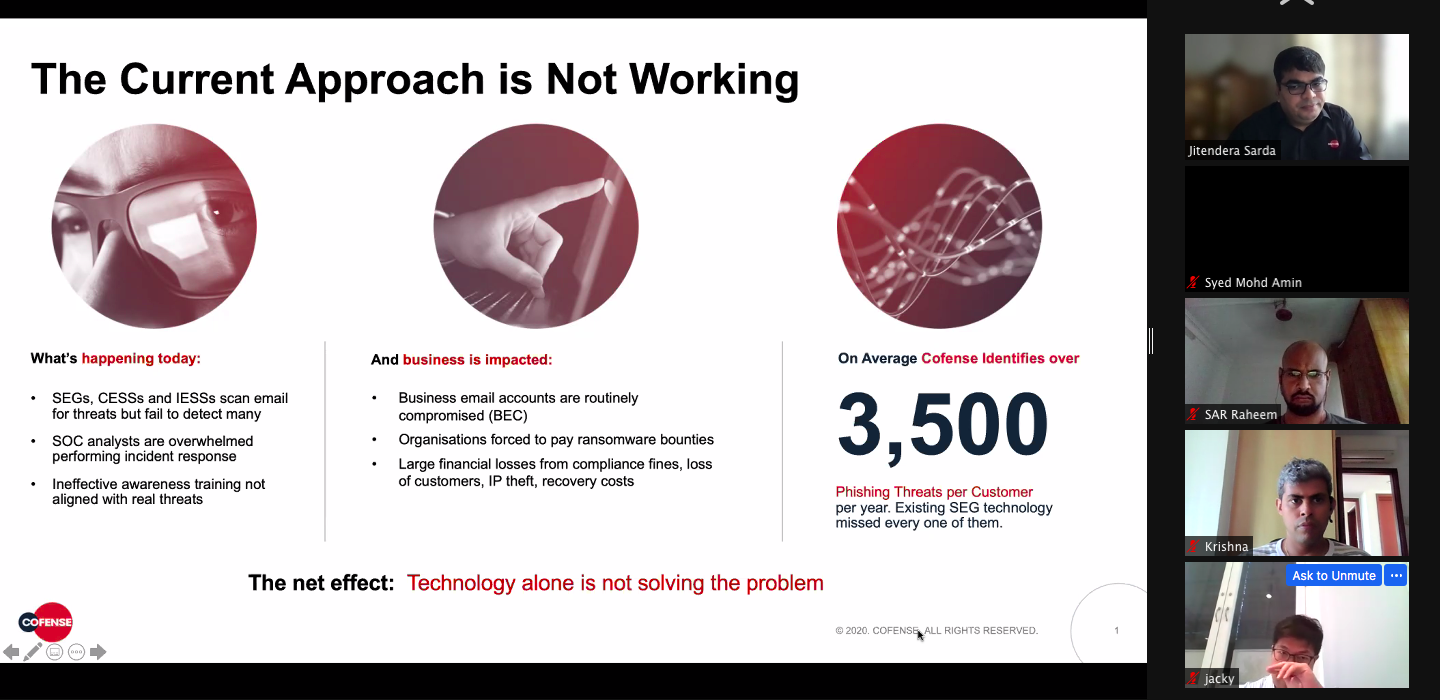
New phishing variants are created daily to evade email gateway security solutions. And once in an environment, they can remain undetected for months. Well-staffed security teams often spend up to 80% of their time analysing phishing threats but with a continuously increasing volume a significant number are unassessed. Other organisations do not have the budget, expertise, or resources required to monitor evolving threat tactics incorporating effective social engineering, patch vulnerabilities on legacy systems, or evolve out-dated workflows.
Credential harvesting: <enter your password here>
The biggest win for hackers is when users fall for ‘genuine looking’ links in phishing emails and unwittingly enter their credentials and in many cases, their single-sign-on (SSO) details. This is called credential harvesting, and it’s a frequently used tactic by threat actors. In fact, according to the Cofense 2021 Annual State of Phishing Report, among the millions of emails the Cofense Phishing Defense Center™ (PDC) analysed, they determined that more than 57% were credential phish.
Once a threat is inside the network, it is important to quickly identify, analyse and remediate the threat. Often the best way to identify threats that have evaded gateway security technology is to rely on the intuition of the people who receive the threat. Accordingly, end user education and training based on real phishing threats is of paramount importance to give security teams visibility of threats that weren’t blocked at the gateway. But reporting is only half of the equation. The second half is analysing the suspected phish and taking appropriate action. A security service like Cofense’s Managed Detection and Response is a great solution. “The PDC has five locations around the world, including a new operational centre based in Melbourne. Our team of highly trained experts manages the incident response and remediation for some of our largest customers globally with millions of end users reporting various threats that evade popular SEGs from Symantec, Proofpoint and Microsoft” notes Dalton Cole, Director of Sales, Australia and New Zealand, Cofense®. “Our team reviews thousands of phishing emails each day that have been reported in environments protected by the leading SEG vendors with an average of 3500 per customer each year”. Dalton also provides some tips and guidance on how to solve the phishing problem:
- Leverage a global network of millions of people actively identifying, reporting suspected phish sharing threat intelligence across teams and with other organisations
- Automate the response to quickly analyse, verify and quarantine phish throughout the organisation
- Use real-world phishing examples in simulation training and awareness programs
- Pick solutions that can be delivered as an integrated suite of products or delivered as managed services
A good phishing detection and response (PDR) platform can detect threats, respond quickly and integrate threat intel onto existing security stacks being used. Cofense delivers a Phishing Detection and Response platform that includes the following solutions:
- Cofense Intelligence™ – Human-vetted phishing intelligence that increases the effectiveness of Cofense Triage and Vision solutions and easily integrates with SIEM, SOAR, TIP platforms.
- Cofense Vision™ – SOC analysts use Cofense Vision to search and auto-quarantine any verified phish throughout the organisation. And Cofense Vision can be fully automated to auto-quarantine any phish based on pre-set policies to stop phishing attacks near instantaneously.
- Cofense PhishMe® – Employees are regularly conditioned to identify suspicious emails using real world phishing simulations and training.
- Cofense Reporter™ – A simple one-click button to report a suspected phish. 26 million people around the world are part of the Cofense network reporting phishing emails and sharing that intelligence across the network.
- Cofense Triage™ – Suspected phish are rapidly clustered and analysed by SOC analysts to queue indicators for remediation in Cofense Triage, Cofense Vision or other technologies.
The Network Effect – Safety in numbers
Cofense combines advanced automation technology with over 26 million people around the world reporting suspected phish. When an attack is detected in one organisation, the intelligence is used to stop attacks in other organisations across Cofense’s network of customers.
“Attackers are diversifying the malware used in phishing campaigns and finding new ways to monetize phishing. In 2020, Cofense identified a major diversification in malware families prominent in phishing which brought an unprecedented amount of disruption, directly leading to an increase in both volume and variety of threat activity. Threat actors continued to advance their tactics, techniques, and procedures to ensure their emails would reach end users throughout the year. Emotet was effectively overtaken by another banking trojan – Trickbot who spread via malicious spam campaigns like spear phishing emails disguised as unpaid invoices or account information updates” says Ryan Jones, Sales Director Asia Pacific, Cofense.
Jones also notes that one tactic Cofense increasingly observed over the past year is the use of multi-stage websites for the user to navigate, also known as layering, that leveraged safe domains. As email security technology adds to and evolves their ability to detect malicious URLs within emails, threat actors are exploiting the use of popular services. These services are often deemed as safe or business critical and are not blocked or restricted.
This is where the network effect comes into the forefront. These attacks can be prevented with the help of a community focused on identifying and fighting these threats Ryan Jones stated, “there’s a lot of data that can be shared to prevent attacks reaching other organisations. The benefit to organisations utilizing the network effect of shared intel will ensure threats known to one, are also known to others that haven’t been attacked yet or haven’t yet reported the attack.”
Cybersecurity Skills and Talent Gap
A report by Forrester [1] noted that enterprise security teams are ‘drowning in alerts’ as the average security-operations group gets more than 11,000 security alerts daily. While the manpower shortages are something businesses cannot solve quickly, advancements in technology are here today. As reported by Not-for-profit AustCyber’s research, Australia is facing a skills shortage of 18,000 cybersecurity experts by 2026 as the nation fights unprecedented attacks on business, government and critical infrastructure. CISOs and CIOs have a daunting task at hand to identify and retain talent in-house while continuing to staff for the increased demand. In many cases, it is not practical to maintain a team of highly skilled, security specialists that focus on simple to very complex incident response activities. A hybrid approach of outsourcing low-value tasks and keeping high value tasks in-house helps develop skilled specialists that stay for longer periods. Tasks that are more repetitive, monotonous and time consuming in nature is generally outsourced or automated, such as level one monitoring or analysis of phishing.
The push towards automation started several years ago and the COVID-19 pandemic has accelerated the release of automation software and systems that are capable of handling processes and actions that were never contemplated before. In terms of cyber security, leveraging Artificial Intelligence, and Machine Learning have enabled fast response to threats often without human intervention.
Conclusion
Cyber criminals target the weakest link in the security chain to get the fastest and largest return on their investment. In most cases, the weakest link is people. With remote work becoming the norm during the pandemic for many organizations, there has been a significant rise in the number of phishing emails and credential harvesting targeting remote workers. There is a need for robust management of threats and to out-human attackers by investments in smarter technology. Legacy software-only security systems are unable to keep up with innovative, human-designed phishing attacks. This calls for the use of advanced Phishing Detection and Response (PDR) platforms, innovated by Cofense, that pairs people with progressive technology to quickly identify phishing campaigns, verify high priority threats and stop the attack within minutes – not days. Organisations managing high volumes of threat assessment with limited resources or expertise can leverage Cofense’s Managed PDR, a managed security service that proactively defends against emerging threats that they see which others don’t. Combined with 26 million people around the world actively identifying and reporting suspected phish, the network effect of using threat intel to stop attacks at every other organisation has become a reality through automation.
As threats evolve and increase in volume, people, process and technology must adapt to automate tasks wherever possible, helping resources to shift their focus on critical matters, retain quality resources and reduce operational costs along the way.
All third-party trademarks referenced herein whether in logo form, name form or product form, or otherwise, remain the property of their respective holders, and use of these trademarks in no way indicates any relationship between Cofense Inc. (“Cofense”) and the holders of the trademarks. Any observations contained in this article regarding circumvention of end point protections are based on observations at a point in time based on a specific set of system configurations. Subsequent updates or different configurations may be effective at stopping these or similar threats.
The Cofense® and PhishMe® names and logos, as well as any other Cofense product or service names or logos displayed on this blog are registered trademarks or trademarks of Cofense Inc.
[1] Forrester – Noted from article by Threatpost
Tags: Advanced Phishing Automation, Cofense, credential harvesting, Cybersecurity, PDR, phishing detection and response



