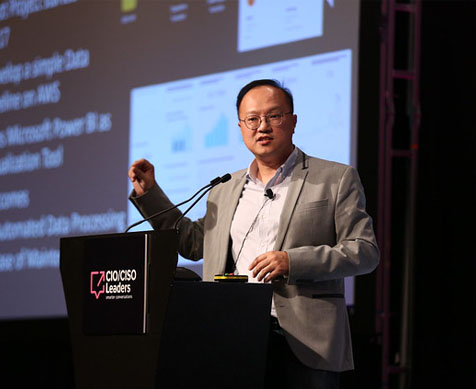
The 10th CISO Leaders Singapore Summit, scheduled for June 25, 2024, at the Marina Bay Sands Expo & Convention Centre in Singapore, will once again serve as the premier gathering for more than 150 of the country’s foremost CISOs, Heads of IT Security, Cyber Security experts, and IT executives.
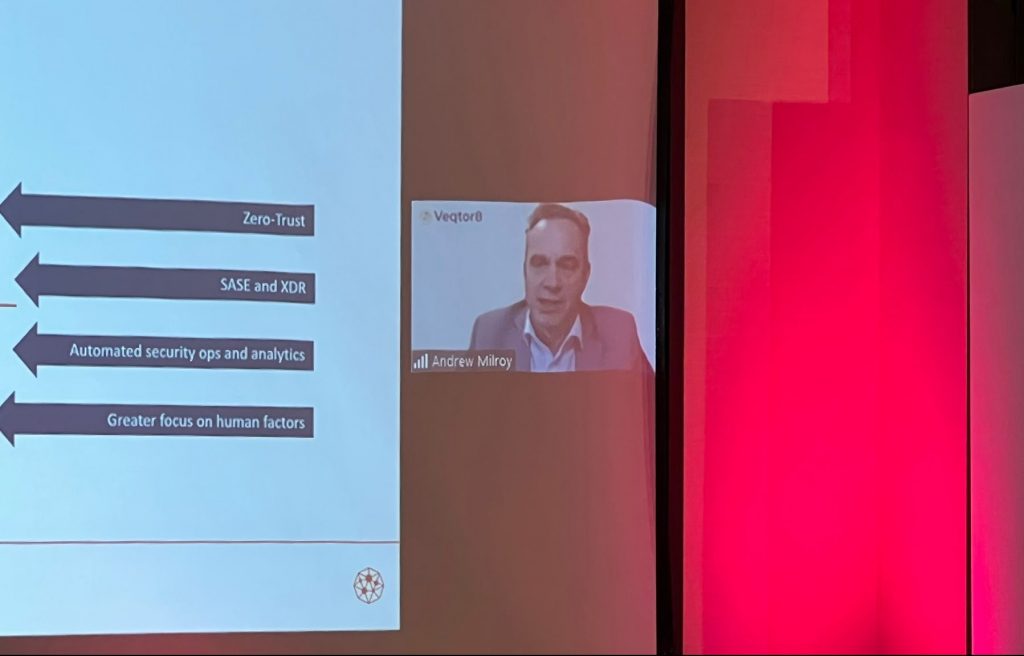
The theme for this year’s summit revolves around “Managing Cybersecurity Complexity in an AI-Driven World“, this message will be conveyed by a distinguished assembly of thought leaders through keynote addresses, panel discussions, interactive workshops, and focused roundtable conversations.
Attendees will have the opportunity to tailor their own agendas, allowing them to optimize their time away from the office by participating in sessions most pertinent to their specific business needs.
Additionally, the networking opportunities available throughout the event will enable senior security executives to engage directly with a carefully curated group of technology vendors through pre arranged business meetings. These vendors will be showcased throughout the day, providing valuable assistance to leading security executives modernisation initiatives. These engagements ensure that businesses remain at the forefront of adopting new technologies, aligning their investment strategies with their overarching business goals.